
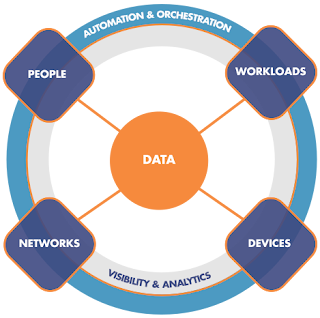
Security landscape has been steadily changing due to proliferation of cloud computing and online services coupled with increasingly mobile workforce. The traditional perimeter and segmentation-based approaches alone no longer match the needs of this new security landscape. With static, well-defined perimeters eroding, organizations need to implement dynamic security approaches that are flexible and continuous in nature. Identity is quickly becoming a new perimeter and frameworks and architectures such as Zero Trust and Secure Access Service Edge (SASE) are redefining how cybersecurity is tackled.
But novel approaches don’t change the fundamentals. That's why I advocate for a time tested defense in-depth strategy that combines multiple and different methods of protection, both traditional and new, and infuses them with the cutting edge Machine Learning (ML) and Artificial Intelligence (AI) technologies that add behavioral dimension and automation to further enhance the practices around core cybersecurity functions (using NIST nomenclature - identify, protect, detect, respond, and recover).
IMHO, defense in-depth strategy doesn’t mean an assortment of technologies (often random) referred to as “best of breed”. Individual components are important, but they are less important than how those components work together. Approaches that rely on tight integration and hyper automation should be preferred; integrated, purpose-built, cloud-native platforms hold the most promise (e.g. SASE).
Organizations are locked in a race with bad actors (a general term for entities such as individuals, criminal enterprises, nation states, etc.) trying to exploit the weaknesses in their systems while being constrained by budgets and availability of skilled resources. That’s why Governance, Risk Management, and Compliance (GRC) activities are essential for understanding what high-value resources that need protecting are, what regulations need to be adhered to, and how much risk an organization is willing to accept.
When contemplating architecture, a good starting point is - what you already own. Incorporating solutions’ native features and controls to the maximum degree possible, will help with driving down the costs while improving integration and automation capabilities.
Finally, having a trusted advisor at your side armed with platform knowledge and lessons learned will save a lot of time and effort.
Be Cyber Safe, not Cyber Sorry!
We are an industry of cryptic names and acronyms 😀 and so I try to spell things out, give them definitions, and illustrate whenever I can -
Definitions:
- User and Entity Behavior Analytics (UEBA) is a type of cyber security process that takes note of the normal conduct of users and entities, then detect any anomalous behavior or instances when there are deviations from these “normal” patterns.
- Continuous Authentication is form of dynamic, risk-based authentication, that relies on continuous measurements such as location, behavior, and biometrics to change the perspective of authentication from an event to a process.
- Security Orchestration, Automation and Response (SOAR) is a solution stack of compatible software programs that allow an organization to collect data about security threats from multiple sources and respond to low-level security events without human assistance.
- Unified Endpoint Management (UEM) is an approach to securing and controlling desktop computers, laptops, smartphones and tablets in a connected, cohesive manner from a single console.
- Endpoint Detection and Response (EDR) is an integrated endpoint security solution that combines real-time continuous monitoring and collection of endpoint data with rules-based automated response and analysis capabilities.
- Threat Intelligence is evidence-based knowledge, including context, mechanisms, indicators, implications, and action-oriented advice about an existing or emerging menace or hazard to assets.
- Threat Hunting is a pursuit of abnormal activity that may be sign of compromise, intrusion, or exfiltration of data.
- Incident Response is an organized approach to addressing and managing the aftermath of a security breach or cyberattack.
- Security Information and Event Management (SIEM) collects and aggregates log data generated throughout the organization's infrastructure, from host systems and applications to network and security devices; then identifies and categorizes incidents and events, as well as analyzes them.
- Zero Trust is an information security framework which states that organizations should not trust any entity inside or outside of their perimeter at any time. All users, services, endpoints, and data flows need to be attested to, authenticated, and authorized.
- Secure Access Service Edge (SASE) is an architecture that converges network and security services into a cloud-based platform, centering on identity of users, devices, and applications.
Zero Trust:

I would like to thanks for sharing this article here. Probing for data cloud storage services Arista Networks Charlotte is the place where you get it. Thank you so much.
ReplyDelete