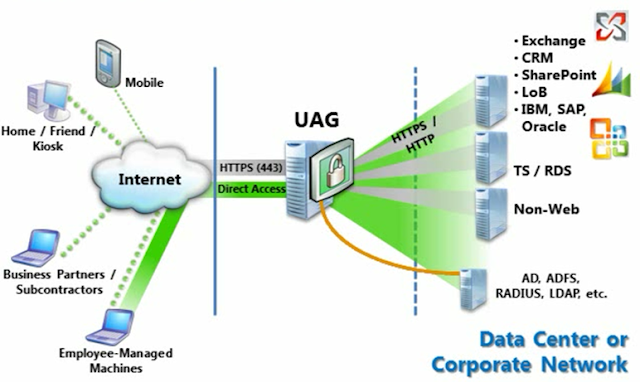
Forefront Unified Access Gateway 2010 delivers comprehensive, secure remote access to corporate resources for employees, partners, and vendors from a diverse range of endpoints and locations, including managed and unmanaged PCs and mobile devices.
Background:
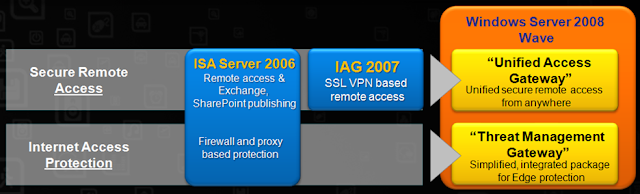
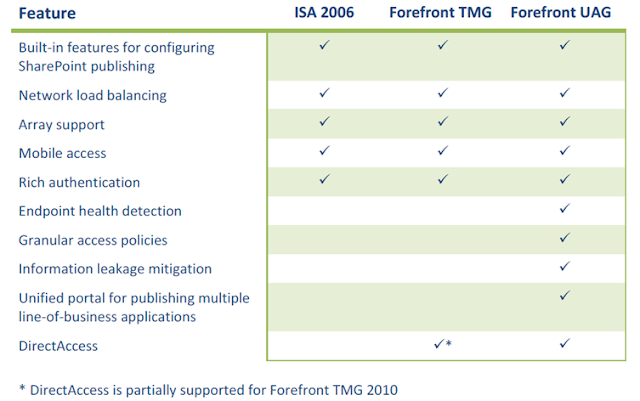
Forefront Unified Access Gateway (UAG) and Threat Management Gateway (TMG) trace their lineage back to other well known Microsoft products - Intelligent Application Gateway (IAG), Internet Security and Acceleration (ISA) Server, Proxy Server, and incorporate technologies from Microsoft acquisitions (Whale Communications). The following outlines latest steps in the UAG and TMG products evolution:
and a brief feature comparison:
Business Ready Security:
Microsoft's Business Ready Security strategy is designed to help organizations of all sizes with managing risk while empowering collaboration and information sharing. At the time of this writing there are five comprehensive solutions that are aligned with this strategy:
- Identity and Access Management
- Secure Collaboration
- Secure Endpoint
- Information Protection
- Secure Messaging
And Unified Access Gateway plays a prominent role within those solutions:
Value Proposition:
Three pillars of UAG's value proposition are -
Solutions Architecture:
UAG's solution architecture exemplifies the value propositions of Anywhere Access, Integrated Security, and Simplified Management: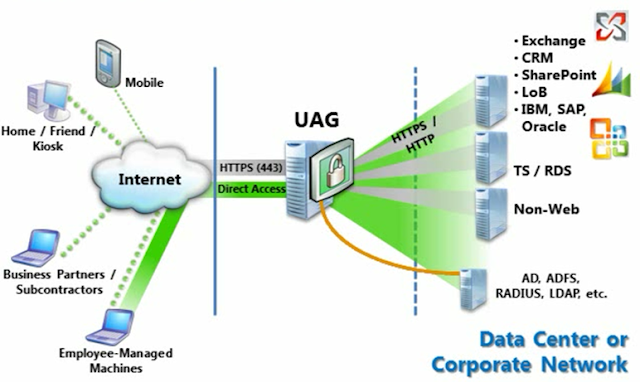
Internal Architecture:
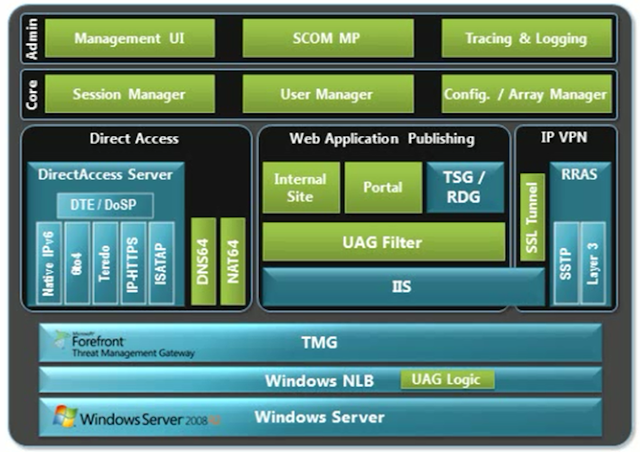
UAG's internal architecture builds upon, extends, or integrates with a number of Windows Server components:
Key Concepts:
- Trunks – primary organizational units (could be HTTP or HTTPS; Portal, Redirect or ADFS), require IP address and FQDN. Contain one or more published applications.
- Applications – built-in services (portal, files access, web monitor), web, client/server and legacy, browser-enabled, terminal/remote desktop services.
- Advanced Services – SSL application tunneling, Network Connector, Secure Socket Tunneling Protocol (SSTP), Direct Access.
- Sessions – various session parameters (timeout, logon/logoff URL, maximum logon attempts, session cleanup).
- Authentication – trunk and application level. Supports: Active Directory, LDAP, RADIUS, RSA Secure ID, WinHTTP, Smart Card/Client Certificate, Other; ADFS 2.0. Enables Single-Sign-On (SSO).
- Clients – endpoint detection, endpoint policies, NAP integration.
Limitations:
- Only web protocols (HTTP, HTTPS) are supported.
- Two part names (such as http://xyz.com) are not supported.
- URLs with different domain names (such as www.yyy.com and www.zzz.com) can’t be published on the same trunk.
For more information refer to the following link.
Common Criteria:
Both Unified Access Gateway and Threat Management Gateway (included with every UAG distribution for firewall protection and support of features such as array management) are common criteria certified:





Comments
Post a Comment